Here is the roll up of the Twitter files part 1. Musk said Part 2 will drop tomorrow.
1/2
2h • 40 tweets • 9 min read
Bookmark Save as PDF My Authors
1. Thread: THE TWITTER FILES
2. What you’re about to read is the first installment in a series, based upon thousands of internal documents obtained by sources at Twitter.
3. The “Twitter Files” tell an incredible story from inside one of the world’s largest and most influential social media platforms. It is a Frankensteinian tale of a human-built mechanism grown out the control of its designer.
4. Twitter in its conception was a brilliant tool for enabling instant mass communication, making a true real-time global conversation possible for the first time.
5. In an early conception, Twitter more than lived up to its mission statement, giving people “the power to create and share ideas and information instantly, without barriers.”
6. As time progressed, however, the company was slowly forced to add those barriers. Some of the first tools for controlling speech were designed to combat the likes of spam and financial fraudsters.
7. Slowly, over time, Twitter staff and executives began to find more and more uses for these tools. Outsiders began petitioning the company to manipulate speech as well: first a little, then more often, then constantly.
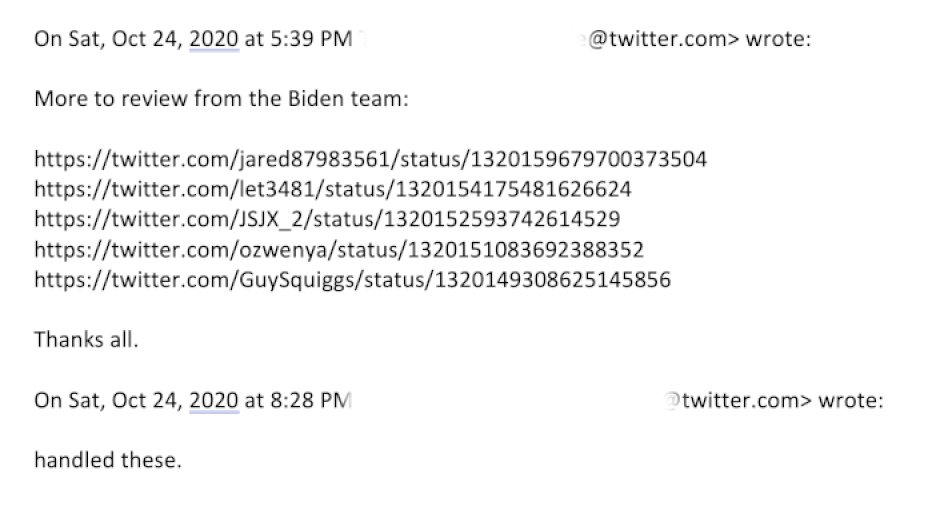
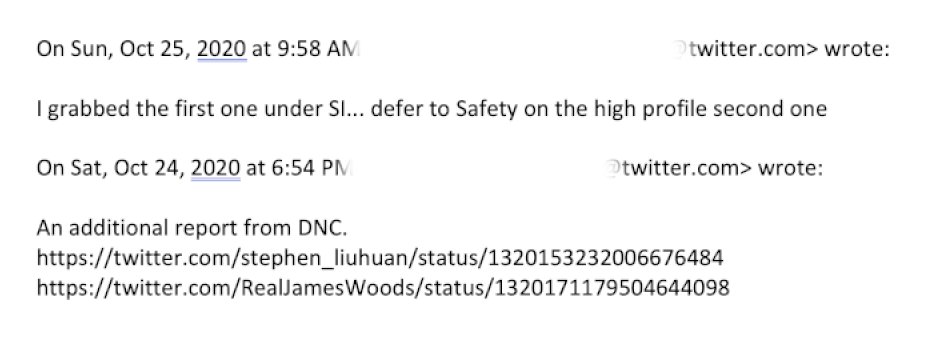
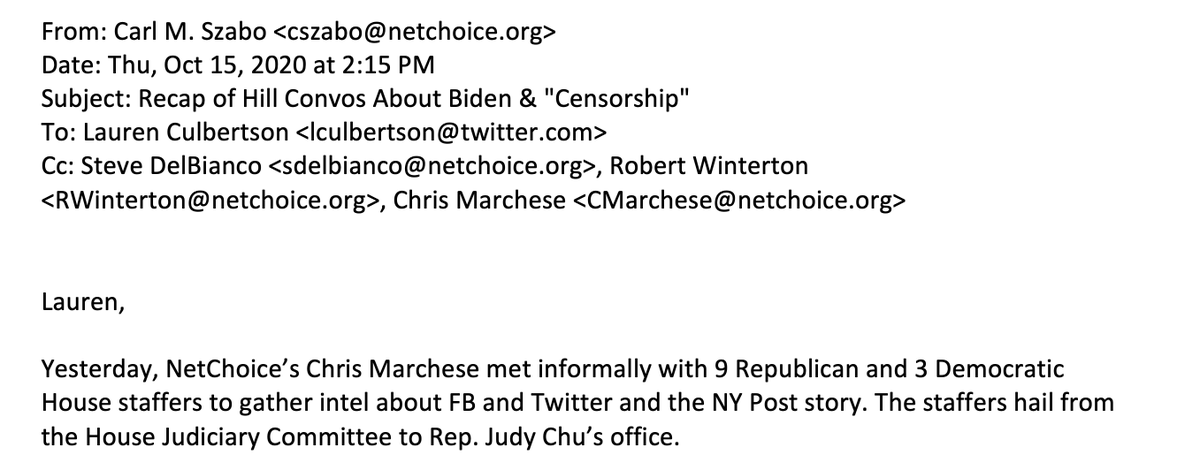
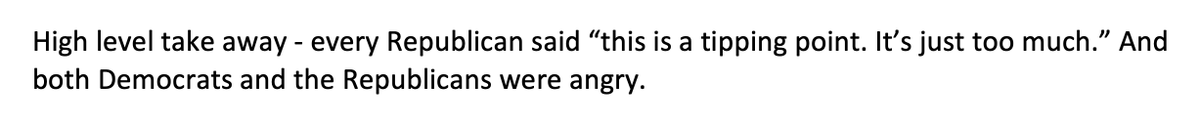
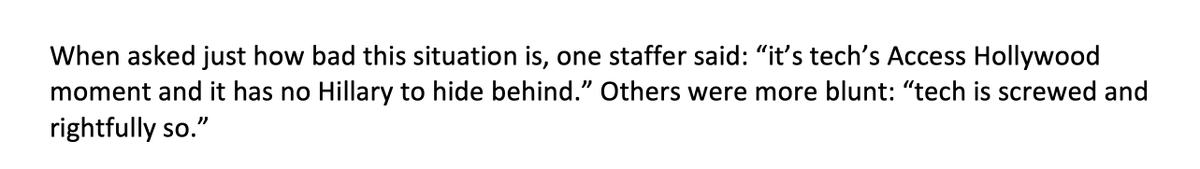
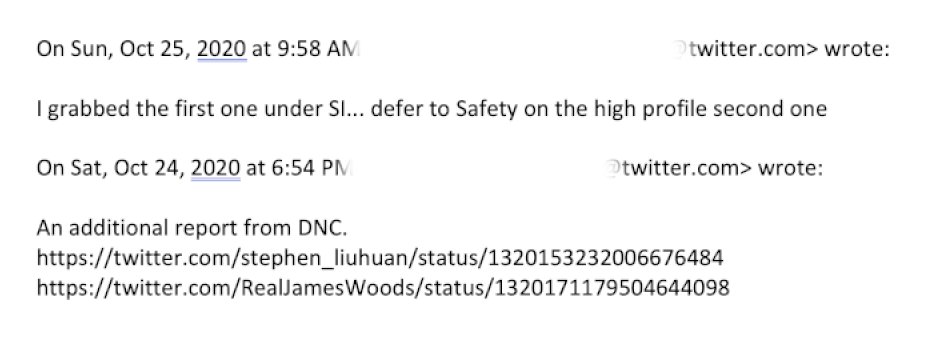
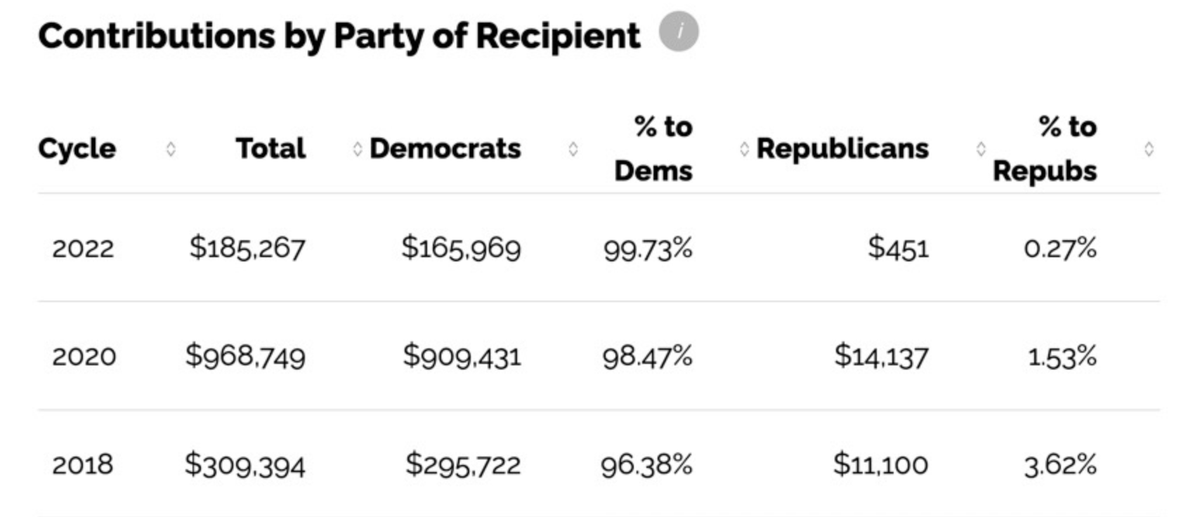
8. By 2020, requests from connected actors to delete tweets were routine. One executive would write to another: “More to review from the Biden team.” The reply would come back: “Handled.”
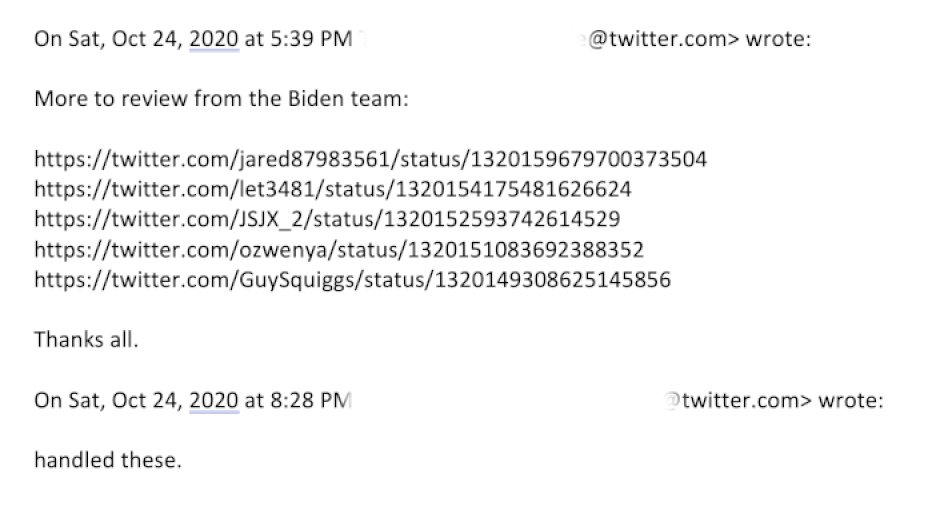
9. Celebrities and unknowns alike could be removed or reviewed at the behest of a political party:
10.Both parties had access to these tools. For instance, in 2020, requests from both the Trump White House and the Biden campaign were received and honored. However:
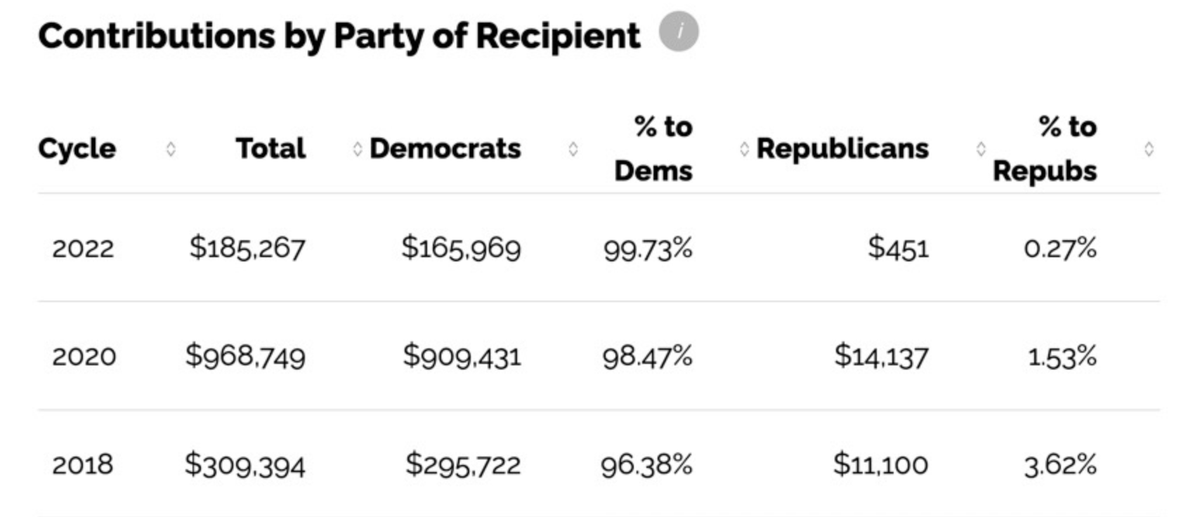
11. This system wasn't balanced. It was based on contacts. Because Twitter was and is overwhelmingly staffed by people of one political orientation, there were more channels, more ways to complain, open to the left (well, Democrats) than the right.
opensecrets.org/orgs/twitter/s…
 Twitter Profile: SummaryTwitter organization profile. Contributions in the 2022 cycle: $185,267. Lobbying in 2022: $970,000. Outside Spending in the 2022 cycle: $0.Twitter Profile: Summary
Twitter Profile: SummaryTwitter organization profile. Contributions in the 2022 cycle: $185,267. Lobbying in 2022: $970,000. Outside Spending in the 2022 cycle: $0.Twitter Profile: Summary
12. The resulting slant in content moderation decisions is visible in the documents you’re about to read. However, it’s also the assessment of multiple current and former high-level executives.
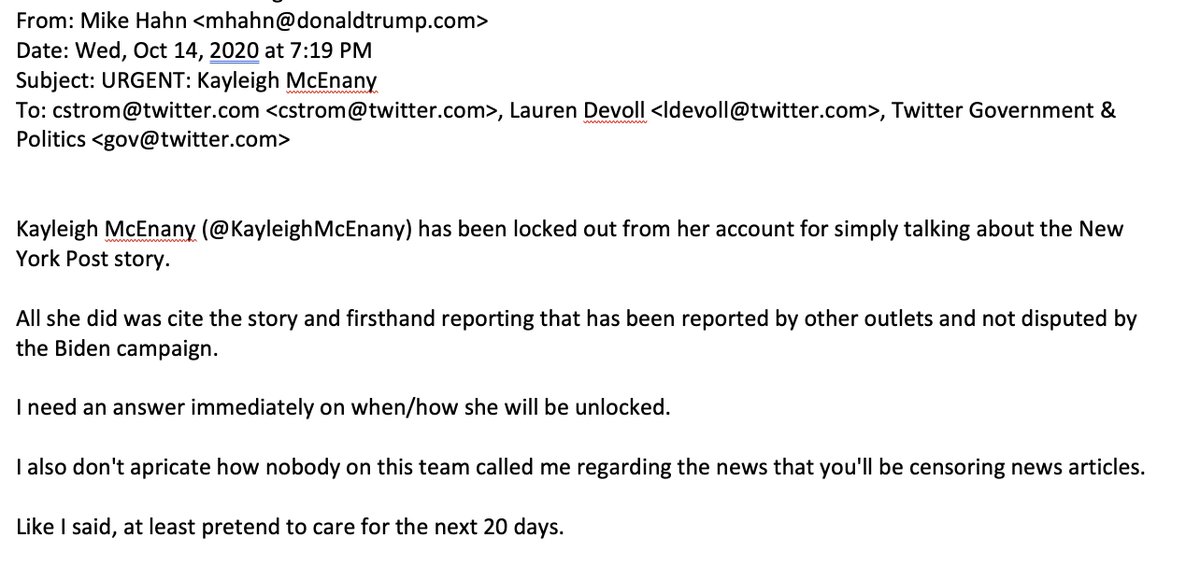
Okay, there was more throat-clearing about the process, but screw it, let's jump forward
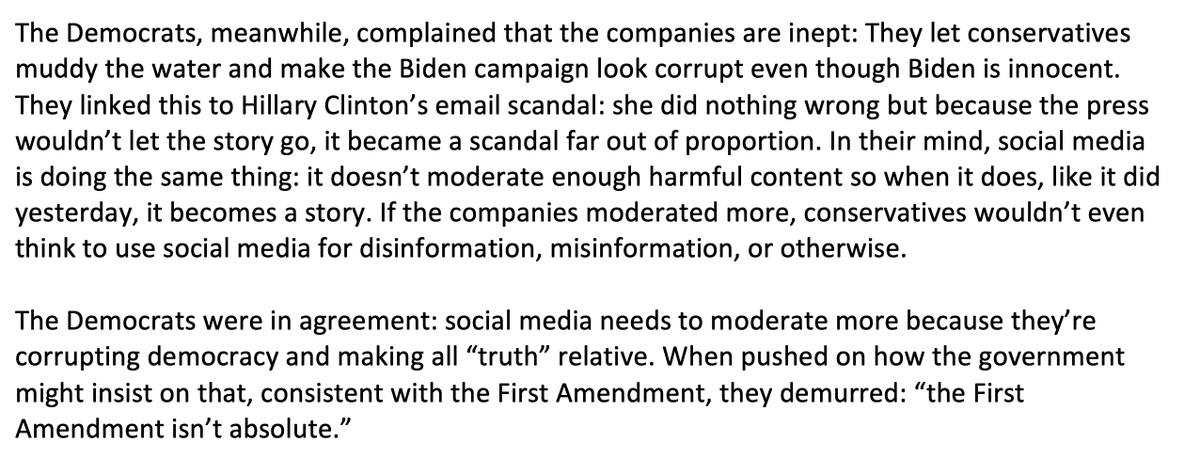
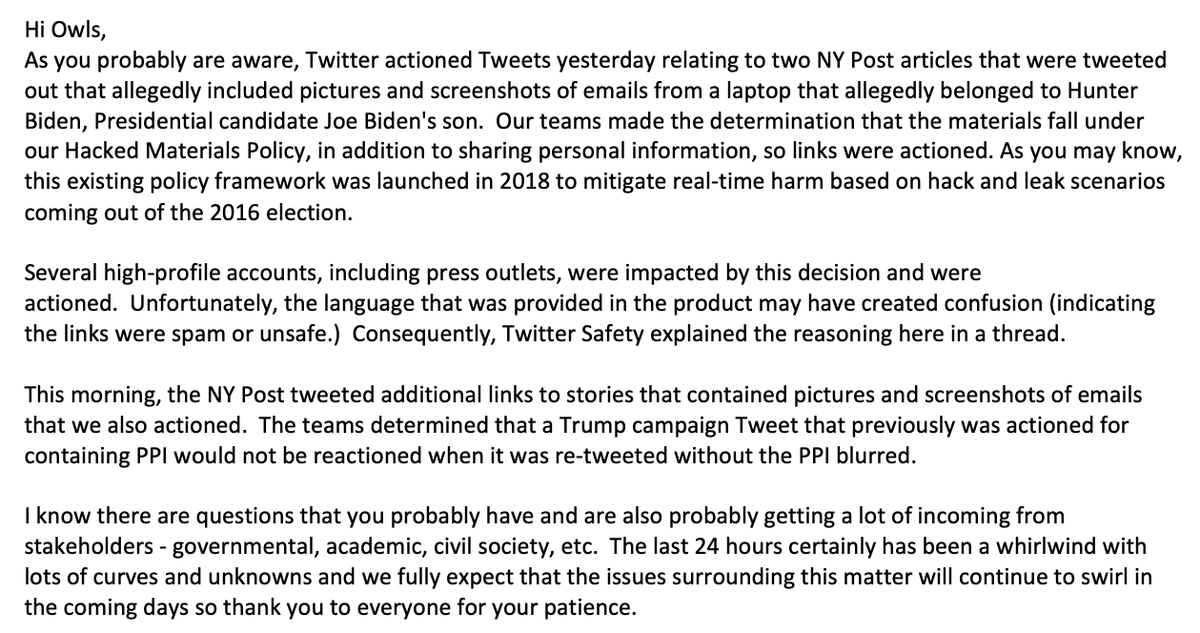
16. The Twitter Files, Part One: How and Why Twitter Blocked the Hunter Biden Laptop Story
17. On October 14, 2020, the New York Post published BIDEN SECRET EMAILS, an expose based on the contents of Hunter Biden’s abandoned laptop:
18. Twitter took extraordinary steps to suppress the story, removing links and posting warnings that it may be “unsafe.” They even blocked its transmission via direct message, a tool hitherto reserved for extreme cases, e.g. child pornography.
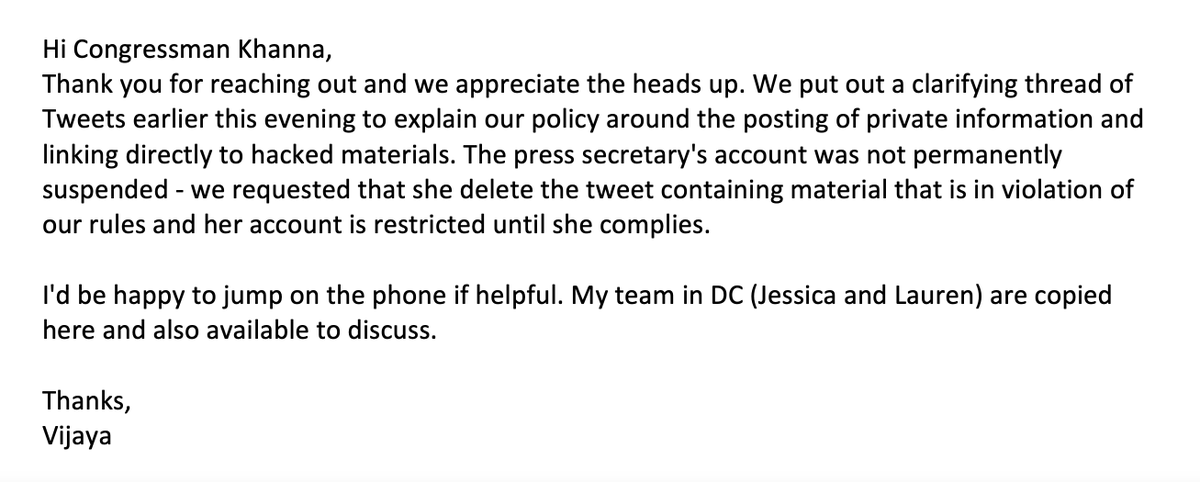
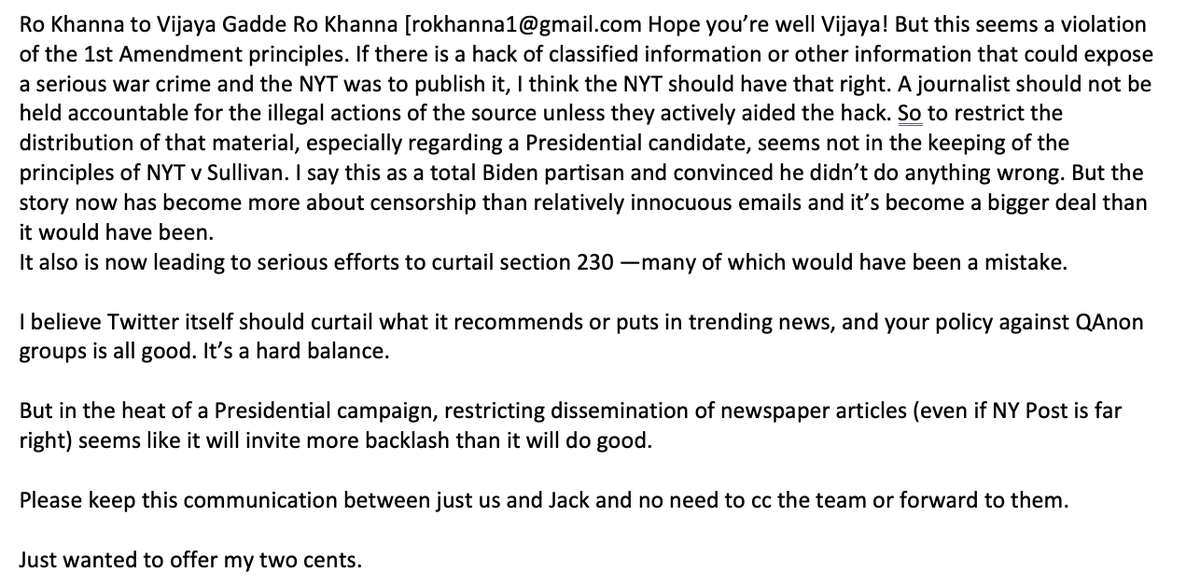
19. White House spokeswoman Kaleigh McEnany was locked out of her account for tweeting about the story, prompting a furious letter from Trump campaign staffer Mike Hahn, who seethed: “At least pretend to care for the next 20 days.”
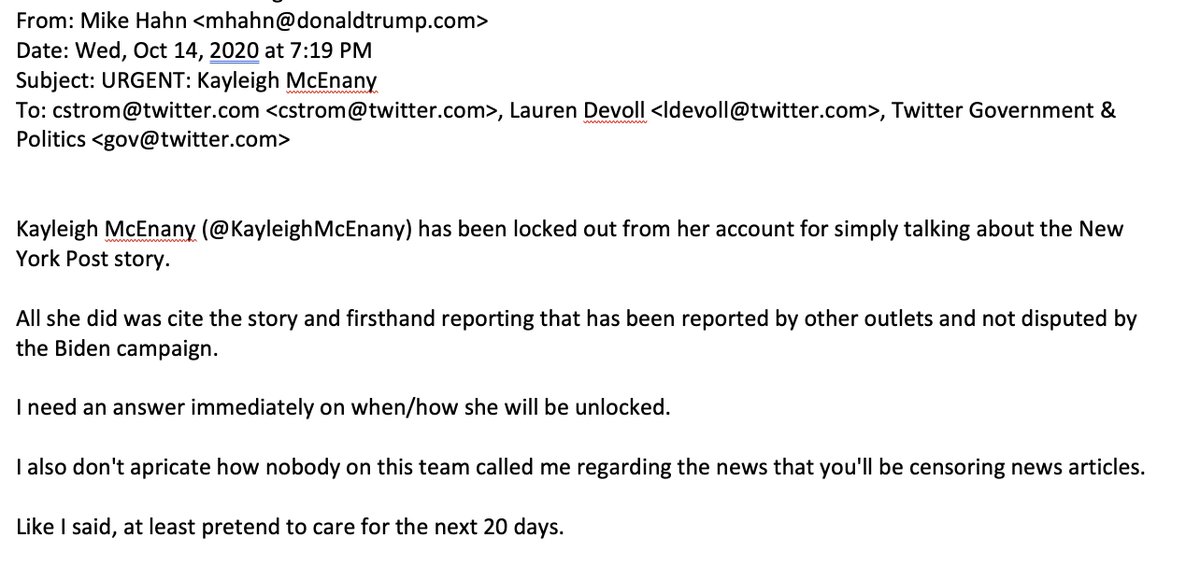
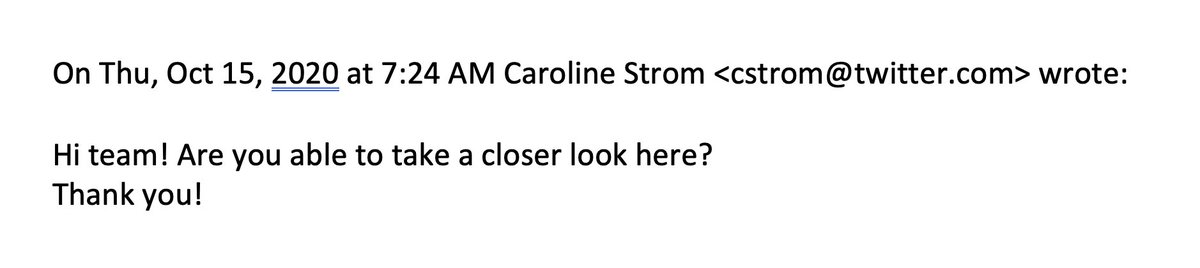
20.This led public policy executive Caroline Strom to send out a polite WTF query. Several employees noted that there was tension between the comms/policy teams, who had little/less control over moderation, and the safety/trust teams:
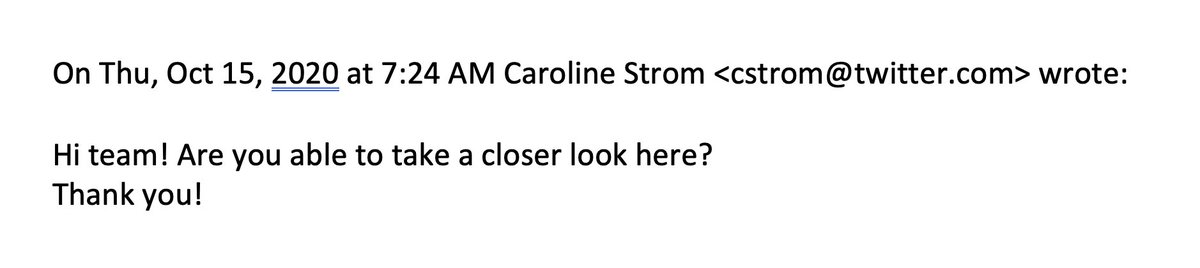
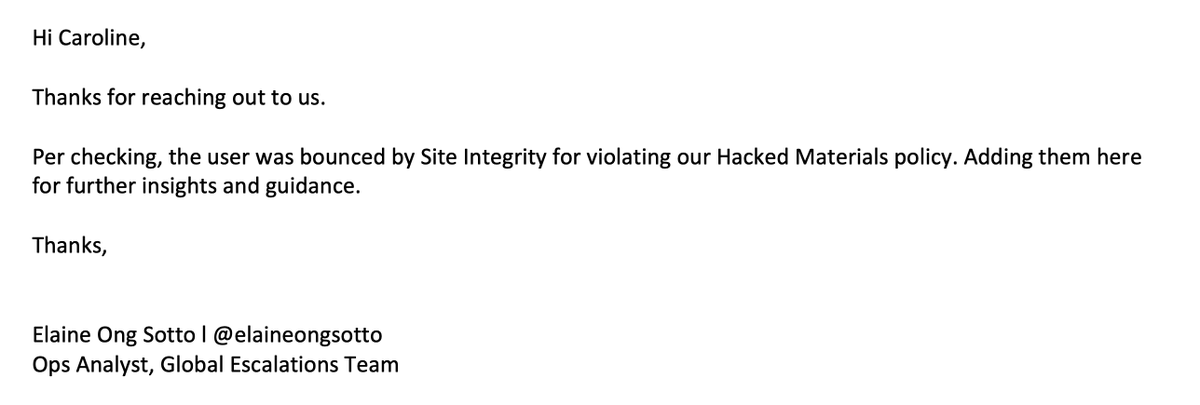
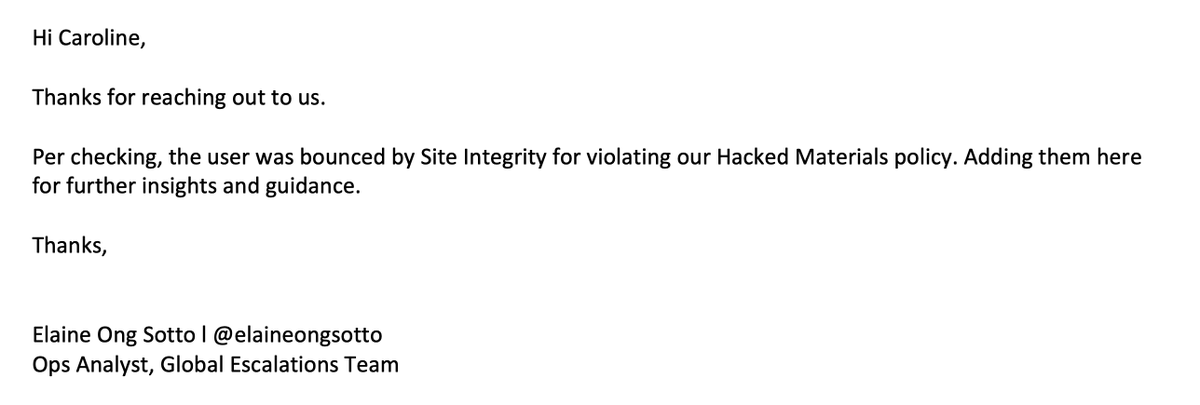
21. Strom’s note returned the answer that the laptop story had been removed for violation of the company’s “hacked materials” policy:
web.archive.org/web/2019071714…
 Distribution of hacked material policyWe don’t condone attempts to compromise or infiltrate computer systems for malicious purposes.Distribution of hacked material policy
Distribution of hacked material policyWe don’t condone attempts to compromise or infiltrate computer systems for malicious purposes.Distribution of hacked material policy
22. Although several sources recalled hearing about a “general” warning from federal law enforcement that summer about possible foreign hacks, there’s no evidence - that I've seen - of any government involvement in the laptop story. In fact, that might have been the problem...
23. The decision was made at the highest levels of the company, but without the knowledge of CEO Jack Dorsey, with former head of legal, policy and trust Vijaya Gadde playing a key role.
24. “They just freelanced it,” is how one former employee characterized the decision. “Hacking was the excuse, but within a few hours, pretty much everyone realized that wasn’t going to hold. But no one had the guts to reverse it.”
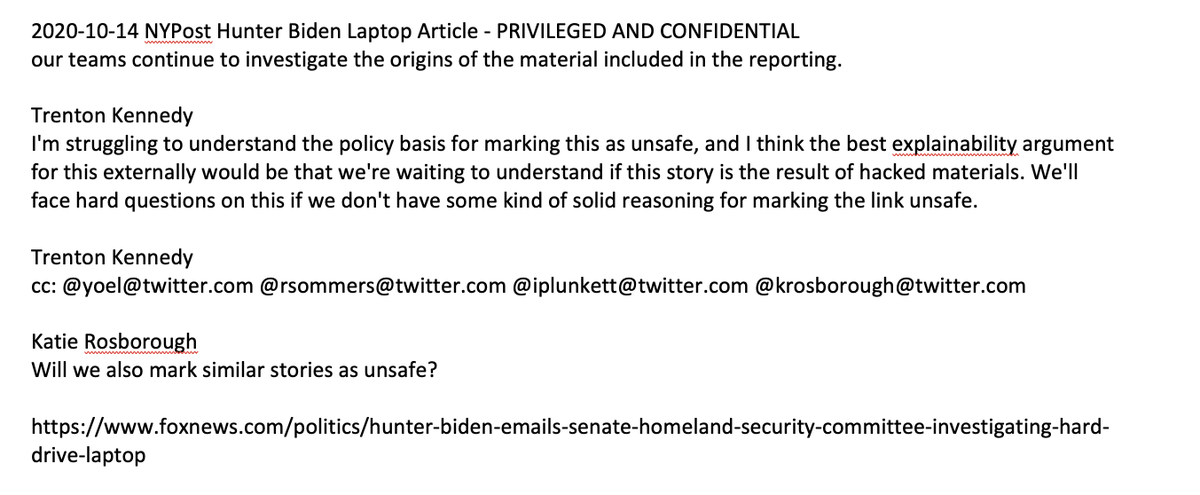
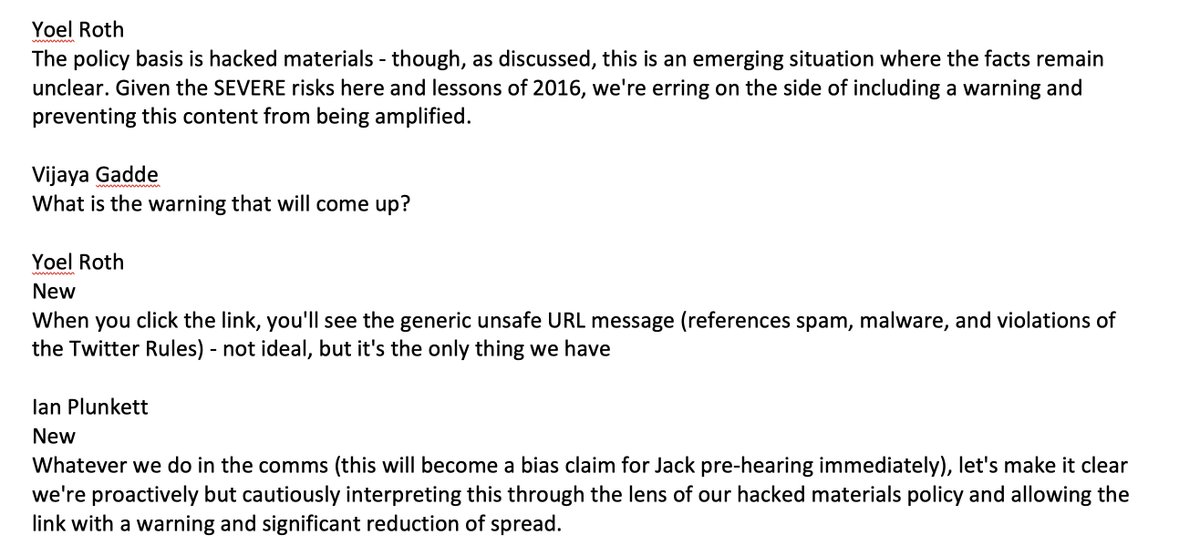
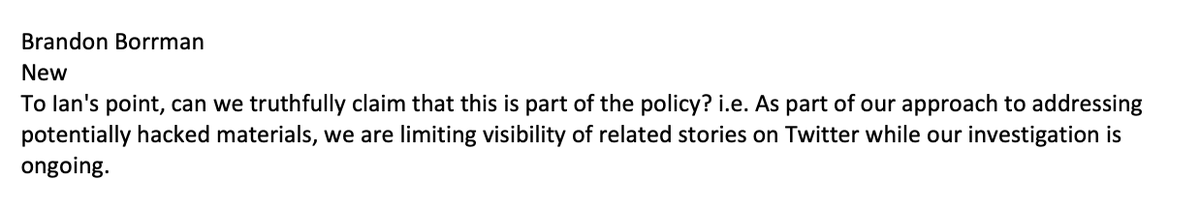
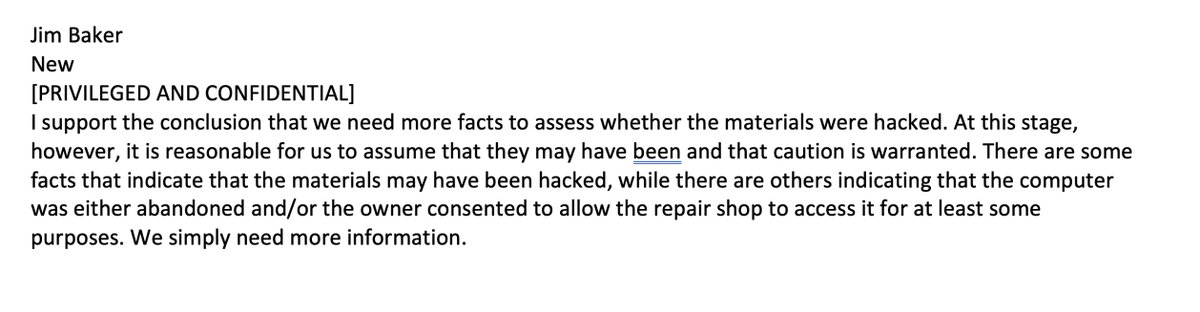
25.You can see the confusion in the following lengthy exchange, which ends up including Gadde and former Trust and safety chief Yoel Roth. Comms official Trenton Kennedy writes, “I'm struggling to understand the policy basis for marking this as unsafe”: